
Exposure Management
Hostile IT environments: how cybercriminals hunt for vulnerabilities across networks
SOC
The rise in popularity of Microsoft Office and attacks on user identities
Strategy
What makes vulnerability management difficult? Key challenges
Strategy
Your Company Has Been Attacked by a Ransomware Group – What Now? An Action Plan
EDR
EDR Is Not Infallible – Techniques for Bypassing Detection Mechanisms

EDR
EDR or Antivirus? What should you choose for your organization
NIS2
KSC and DORA in practice: challenges, technologies, and processes
Strategy
Threat Hunting – a proactive cybersecurity strategy for organizations
SOC
What Is SOC? Key areas of operation and technologies

Threat Intelligence
What is Cyber Threat Intelligence and how does it support organizations in protecting against threats?
SOC
“There are no constants in cybersecurity” – A conversation with Michał Horubała, SOC360 Director
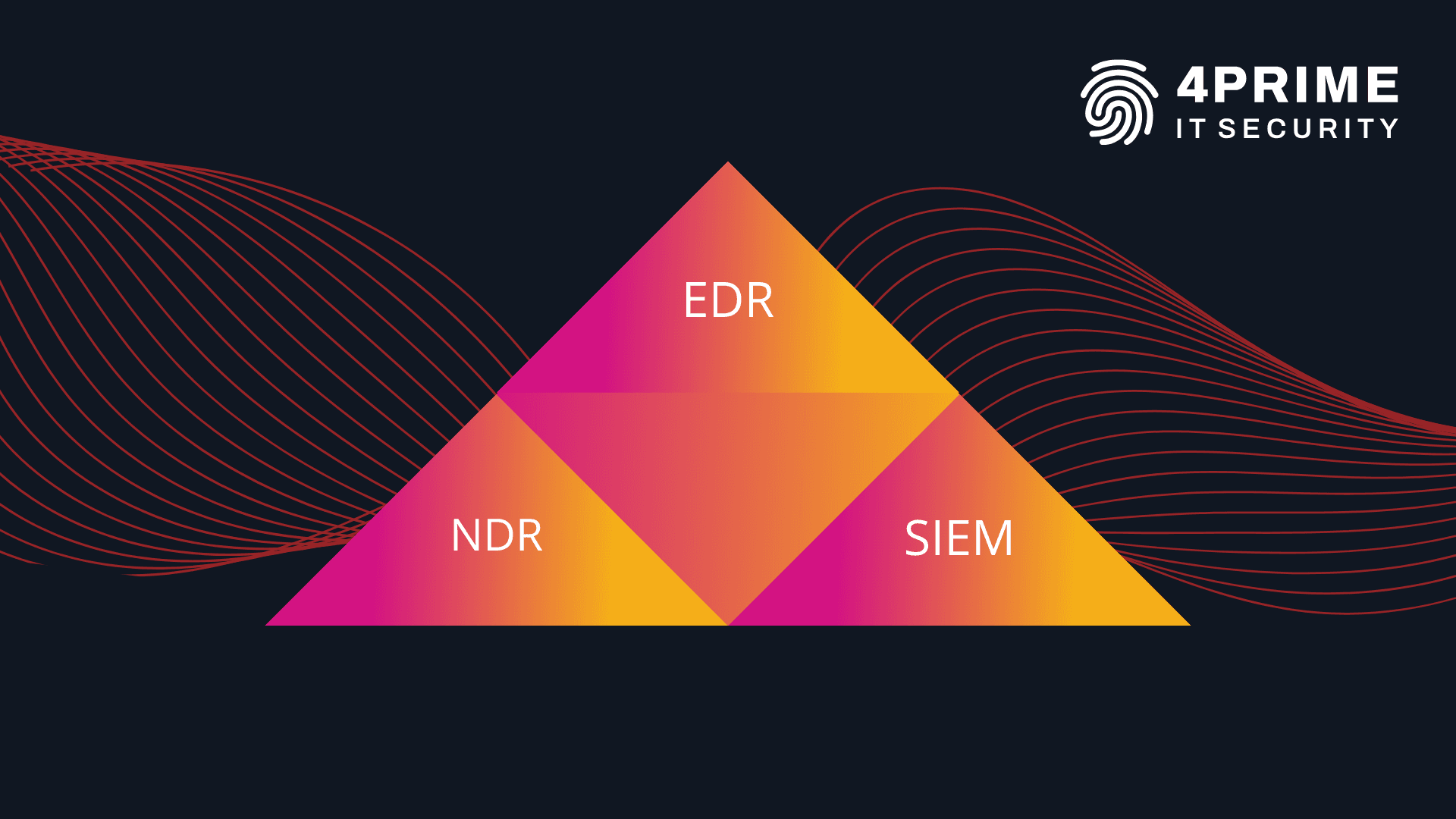
EDR
◦NDR
◦SIEM