NDR Systems -
Network Detection and Response
What is NDR?
NDR is the core of network traffic protection. It combines advanced analytics with full visibility into an organization’s internal infrastructure. It effectively identifies issues related to misconfigurations, security policy violations, performance drops, and emerging attack techniques.
NDR as a mandatory complement to an IT security strategy
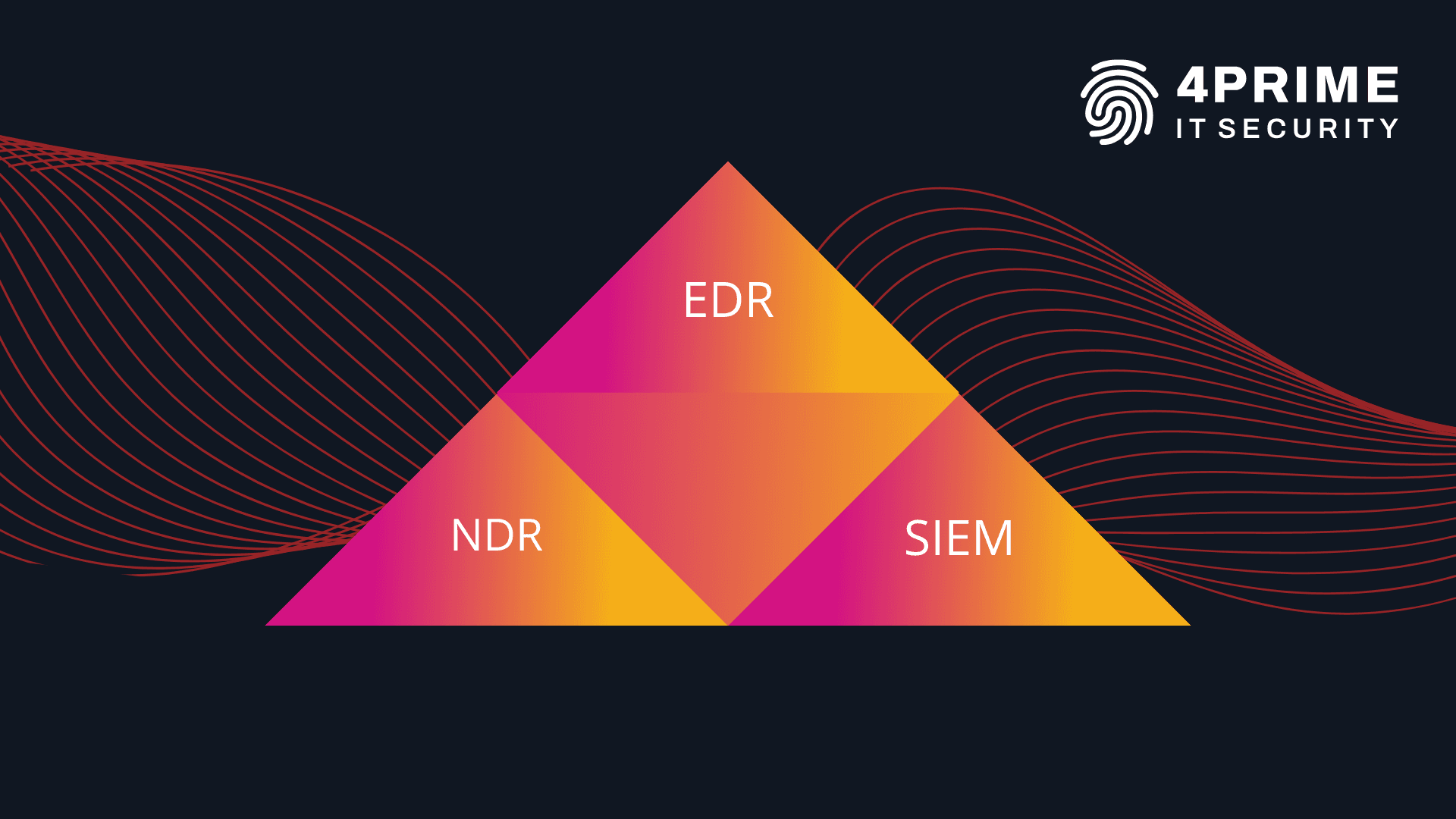
In conversations with our clients, we often emphasize that EDR systems address about 70% of attack techniques described in the MITRE ATT&CK framework.
To cover another 20%, organizations should consider implementing an NDR system. NDR monitors all network traffic in real time, enabling the detection of suspicious activities such as unusual connections or sudden, large data transfers.
By using signatures and heuristics, NDR identifies attack techniques including lateral movement and data exfiltration. Building detailed user behavior profiles and collecting rich network telemetry makes it possible to detect unauthorized activities, while integration with other security tools—such as EDR and SIEM—provides a comprehensive view of threats.
NDR system features
Implementation services for modern NDR solutions from our partners
We have the most extensive experience in the market in implementing NDR systems, supported by the delivery of demanding deployments in complex, international environments. This enables us to tailor the solution to the specific needs of each organization, ensuring effective protection against real-world threats.


SOC service based on EDR and NDR systems
As the SOC360 team (Security Operations Center), we work with EDR/XDR and NDR tools. EDR solutions enable our analysts to precisely track events occurring on endpoints and respond quickly to incidents—for example, by immediately stopping malicious processes and isolating them in quarantine.
Because NDR systems monitor network traffic, they allow us to detect events that may have been missed by other tools.
We also frequently correlate data from different systems using SIEM platforms, which play a complementary role in our operations.
In addition, we have a laboratory for detonating and analyzing suspicious files whose functions and purposes are unknown, as well as a lab for testing new technologies so we can evaluate new systems before deployment.
We are also supported by a development team that customizes ticketing systems, builds automation, and writes scripts that assist in incident analysis and internal data processing.