EDR Systems -
Endpoint Detection and Response
What is EDR?
EDR-class systems focus on real-time monitoring and securing network endpoints such as computers, servers, and mobile devices.
EDR introduces an innovative approach to security telemetry that goes beyond traditional log and alert collection—it analyzes detailed behavioral data, enabling more accurate differentiation between normal user activity and potential threats.
Incident monitoring with EDR systems is a foundation of a modern SOC (Security Operations Center). Unlike traditional solutions based solely on SIEM, EDR gives analysts the ability to respond to incidents more effectively.
EDR addresses 70% of attack techniques
EDR is a cornerstone of IT security—it covers most of the attack techniques described in the MITRE ATT&CK matrix. It enables precise tracking of events occurring on endpoints, which is especially important because cybercriminals often leave traces there. In addition, EDR systems provide:
EDR system capabilities
Real-time threat detection – Thanks to built-in AI and Machine Learning (ML) mechanisms, EDR systems can quickly detect anomalies at the operating system level. They identify known threats, new attack techniques, and advanced methods of concealing malicious code, such as polymorphism and obfuscation.
Automated response and post-incident analysis – EDR systems automatically isolate an infected device, file, or process immediately after a threat is detected. Using the collected telemetry data, they help organizations address vulnerabilities and continuously improve their IT security infrastructure.
System rollback to the pre-attack state – EDR systems support business continuity by minimizing downtime and the losses caused by incidents.
Modern EDR solutions from our partners
We have the most extensive experience in the market in deploying EDR systems, backed by complex implementations in demanding, international environments. This enables us to tailor each solution to the specific needs of an organization, ensuring effective protection against real-world threats.





SOC service based on EDR
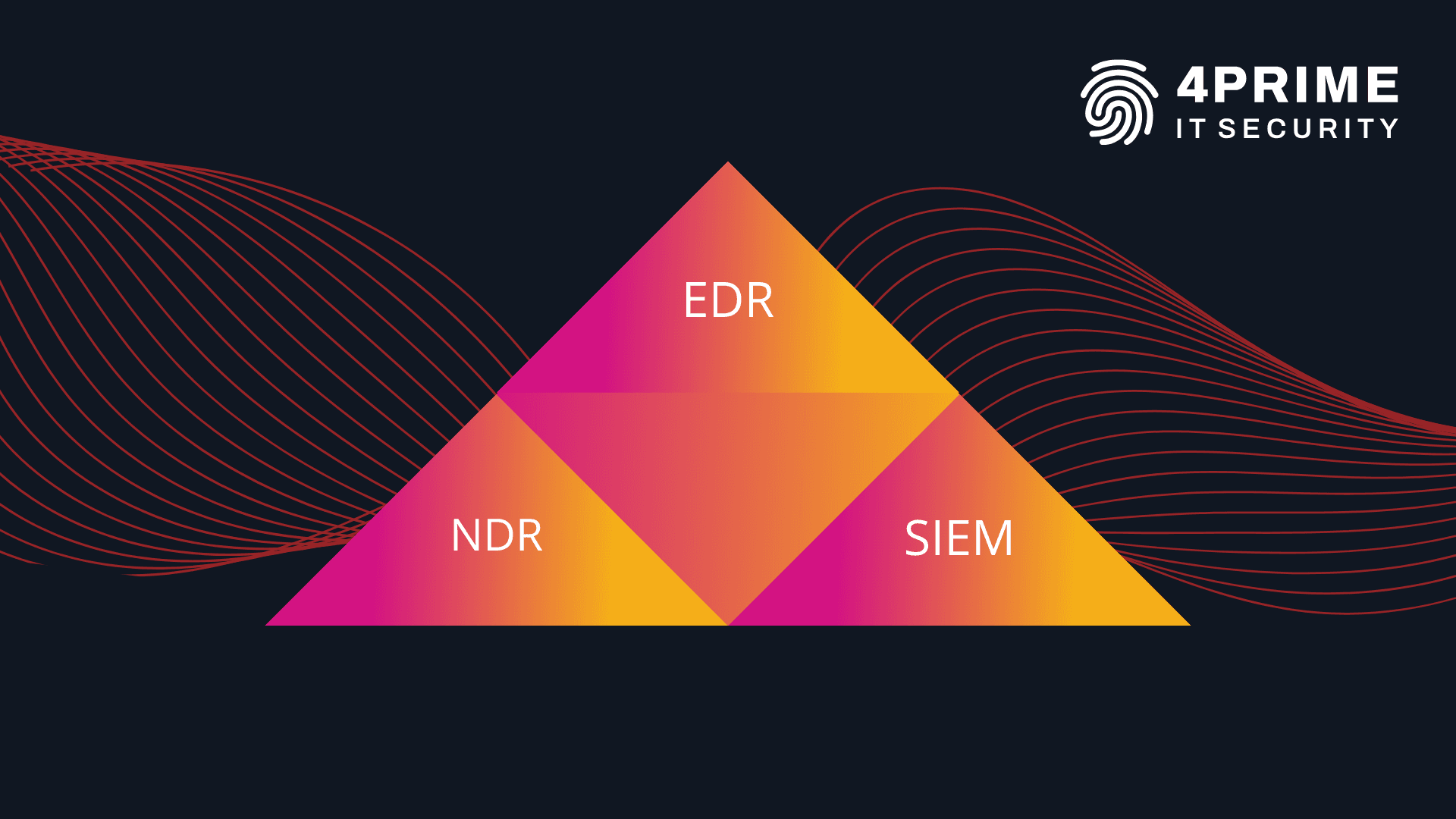
As the SOC360 team, we work with EDR/XDR tools that allow us to precisely track events occurring on endpoints.
Thanks to EDR solutions, we can respond quickly to incidents—for example, by immediately stopping malicious processes and isolating them in quarantine. In addition, we use NDR systems that monitor network traffic, enabling us to detect events that may have been missed by other security tools.
We also frequently correlate data from different systems using SIEM platforms, which play a complementary role in our operations.
Moreover, we have a laboratory for detonating and analyzing suspicious files whose functions and purpose are unknown, as well as a lab for testing new technologies so we can evaluate new systems before deployment.
We are also supported by a development team that customizes ticketing systems, builds automation, and writes scripts that assist in incident analysis and internal data processing.