The rise in popularity of Microsoft Office and attacks on user identities
Mass adoption of Microsoft Office 365 has made user identity the primary attack target. Over the past two years, the number of incidents related to account compromise in Microsoft environments has nearly doubled, while their effectiveness remains high. A typical incident involves silent access lasting days or weeks, Outlook rules used to siphon off correspondence, and then escalation: financial fraud, further account takeovers, or resale of access to other criminal groups. User education and anti-phishing systems help, but they do not fully solve the problem—attackers successfully bypass detection mechanisms using CDNs, delayed infrastructure activation, and techniques such as QR phishing.
The rise of Microsoft Office adoption and attacks on user identities
In 2023, we observed the final stage of a major migration wave toward Microsoft Office 365 collaboration platforms. Today, most of our clients use cloud environments in a hybrid model. Microsoft Outlook, OneDrive, SharePoint, Entra, and Azure have become so widely adopted that they appear—at least to some extent—in 95% of the organizations we work with.
At the same time, around the turn of 2024, the number of incidents related to attacks on user identities in the Microsoft systems we monitor nearly doubled and has remained at a high level in recent months. These attacks are highly effective and account for a significant share of incidents that require rapid response from our team.
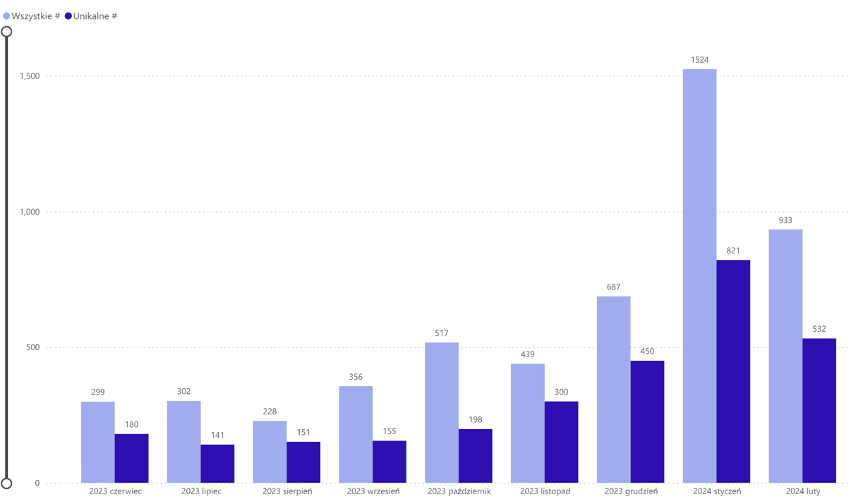
As shown above, cybercriminal organizations have quickly adapted to the new opportunities created by direct access to corporate resources without the need to breach traditional network perimeter defenses. This shift is directly reflected in the growing volume of attacks targeting user identities.
Threats related to user identity attacks
Phishing
Email has long been one of the most commonly exploited attack vectors. In previous years, it was primarily used to deliver malware that opened the door to organizational networks and data. In this area, we have seen steady progress in social engineering quality, infrastructure preparation, and the use of sophisticated evasion techniques to bypass security systems.
However, the area where we have observed the greatest increase in threats involves messages persuading users to click a link that leads them to log in to corporate Office 365 services via infrastructure controlled by cybercriminals. These attacks allow attackers to bypass additional 2FA protections and result in session token theft. As a result, threat actors gain access to user accounts and subsequently leverage them for further activities.
Abuse of credentials obtained from other sources
A large portion of the incidents we analyze involve access to Office 365 user accounts using credentials obtained through other means. These credentials typically come from data breaches or stealer-type malware installed on computers and mobile devices. Such activity manifests as automated login attempts that occur in small volumes and are often not reported by security systems. The goal is to gain access to accounts without 2FA enabled or to trigger user approval via push notifications.
What does a typical identity breach incident look like?
Typical incidents related to the above attack vectors follow a similar pattern:
- After gaining access to a user account, threat actors quietly observe email correspondence and analyze available resources for an extended period (usually one to two weeks).
- Outlook configuration rules are often created to forward selected correspondence to attacker-controlled services. These actions are intended to exfiltrate data or conceal further activity.
- Messages are sent from the compromised account on behalf of the user. This can lead to the following consequences:
- Convincing employees or partner organizations to pay invoices with altered bank account numbers.
- Expanding attacker access by compromising additional accounts.
- Selling obtained access to other groups (for example, ransomware operators).
How to counter user identity attacks?
Conditional access
Organizations using Office 365 can introduce additional account security controls by implementing conditional access mechanisms. Unfortunately, this involves additional licensing costs. Moreover, access restrictions negatively affect user experience, and handling related support tickets and configuration management requires extra IT resources.
User education
The most obvious solution is user education, which can take various forms. One of the most effective approaches currently in use is a well-designed and properly managed phishing simulation program. However, preparing and managing such simulations, analyzing results, and developing training materials all require additional resources. Organizations must also purchase a commercial solution or deploy an open-source platform.
Unfortunately, even the best education and simulation systems do not guarantee success. Many incidents we have analyzed involved well-crafted identity attacks against executives, who are often reluctant to participate in training programs.
Anti-phishing systems
The cybersecurity market offers a wide range of systems designed to detect and block phishing attempts. These systems require license purchases, typically offered in a subscription model based on the number of protected mailboxes. Deployment itself is usually straightforward and limited to simple integration with Office 365.
However, organizations must be prepared to handle false positives and complaints from users who did not receive urgent messages incorrectly classified as dangerous. From our experience, many solutions available on the market demonstrate moderate or low effectiveness.
To redirect users to credential-harvesting pages, attackers use CDN (Content Delivery Network) infrastructure, where redirection depends on attacker-defined parameters such as operating system, location, or application type. As a result, link-inspection systems are redirected elsewhere than the actual user destination. In most serious incidents handled by our team, the infrastructure used in the attack was activated only during or immediately after message delivery and therefore was not classified by Threat Intelligence sources.
We have also encountered several campaigns using QR codes. This technique has proven surprisingly effective. A user may receive a link leading, for example, to a shared Evernote note (which appears harmless to security systems). Only within the note does the user find another link redirecting them to a SharePoint document via attacker-controlled infrastructure. As a result, we observe little difference between environments equipped with additional anti-phishing tools and those relying solely on built-in Office 365 protection mechanisms.
How to detect incidents?
The dynamic nature of identity attacks targeting Office 365 requires careful verification of every alert, as the consequences of negligence can be severe. This analysis requires access to system telemetry to investigate user account activity and must be performed by qualified personnel.
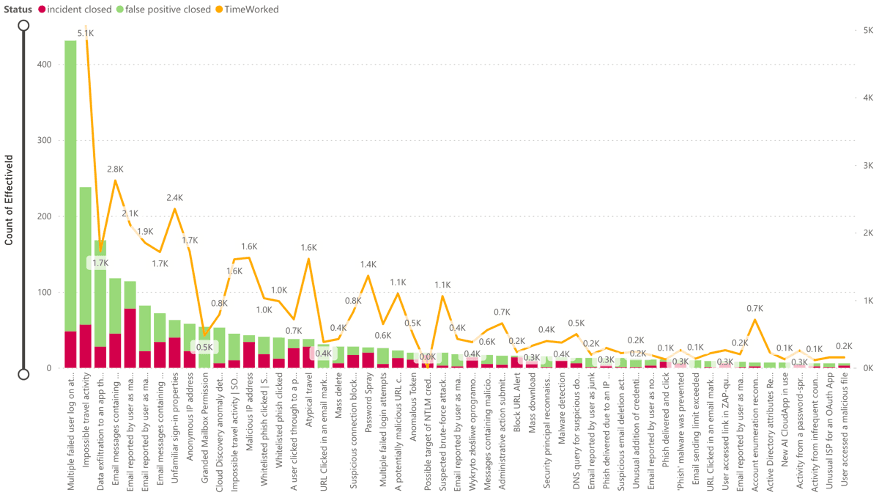
At SOC360, we use security mechanisms available within the Office 365 platform—Defender for Cloud Apps, Defender for Office 365, and Defender for Identity—to detect attempts to compromise user identities. We monitor detection rules such as Impossible Travel Activity, Unfamiliar sign-in properties, as well as many custom rules created by our team to identify suspicious activity. We also analyze incidents reported by users.
How to respond to incidents?
Once an incident is confirmed—meaning unauthorized access to a user account—the next step is to determine subsequent attacker actions and their impact. To do this, the SOC team must analyze telemetry available in Microsoft Security systems to determine, among other things:
- Whether the incident may affect additional users (who else received similar messages in recent days, and what happened afterward).
- Whether suspicious IP addresses were active on other accounts.
- Which resources were accessed.
- Whether messages were sent from the compromised account (confirmation opens additional investigation threads).
- Whether new Outlook rules were created.
As part of the response, attacker access to the account must be immediately terminated. This requires forcing session termination, changing passwords, or blocking affected user accounts. These actions are effective if performed within a few hours of attackers gaining access.
Summary
Over the past two years, we have observed a significant increase in attacks targeting user identities within the Microsoft Office 365 platform. Cybercriminal groups have adapted to the growing popularity of this service during and after the pandemic. The accessibility and convenience of this modern collaboration environment naturally create new opportunities for attackers.
As a result, the SOC360 team is facing a growing wave of attacks whose creativity, preparation, and execution are almost admirable. The effectiveness of these attacks against Polish organizations is also increasing. AI platforms help cybercriminals overcome language barriers, which previously—combined with the innate skepticism of Polish users—posed an additional challenge.
Fortunately, these attacks can be effectively detected, and proper response allows organizations to avoid their consequences, provided that continuous monitoring and alert analysis are in place, along with proper configuration of detection mechanisms within Microsoft Security systems.
If you want to strengthen cloud security in your organization, contact us.
This article was prepared entirely by cybersecurity experts—without the use of artificial intelligence tools.
Text autor: