Modern cybersecurity can no longer rely solely on antivirus solutions and SIEM. EDR and NDR provide real detection and response to advanced threats — EDR alone addresses approximately 70% of attack techniques defined in the MITRE ATT&CK framework, making it a foundational layer of endpoint security. SIEM remains a valuable complement for log correlation and context, but without EDR and NDR it does not deliver comprehensive protection.
The dynamic development of technology, in addition to numerous business benefits, also brings new and increasingly sophisticated threats to IT infrastructure security. The consequences of security incidents are often severe and may lead to operational disruptions, financial losses, or damage to a company’s reputation.
For this reason, building an effective cybersecurity strategy by implementing protection at all levels—from endpoints to the network—should be a top priority for organizations.
Our experience shows, however, that many companies still rely solely on antivirus solutions, next-generation firewalls (NGFW), or SOC services based exclusively on SIEM systems. Meanwhile, today’s attack methods, which leverage complex techniques rather than predefined signatures alone, clearly demonstrate that this approach is no longer sufficient.
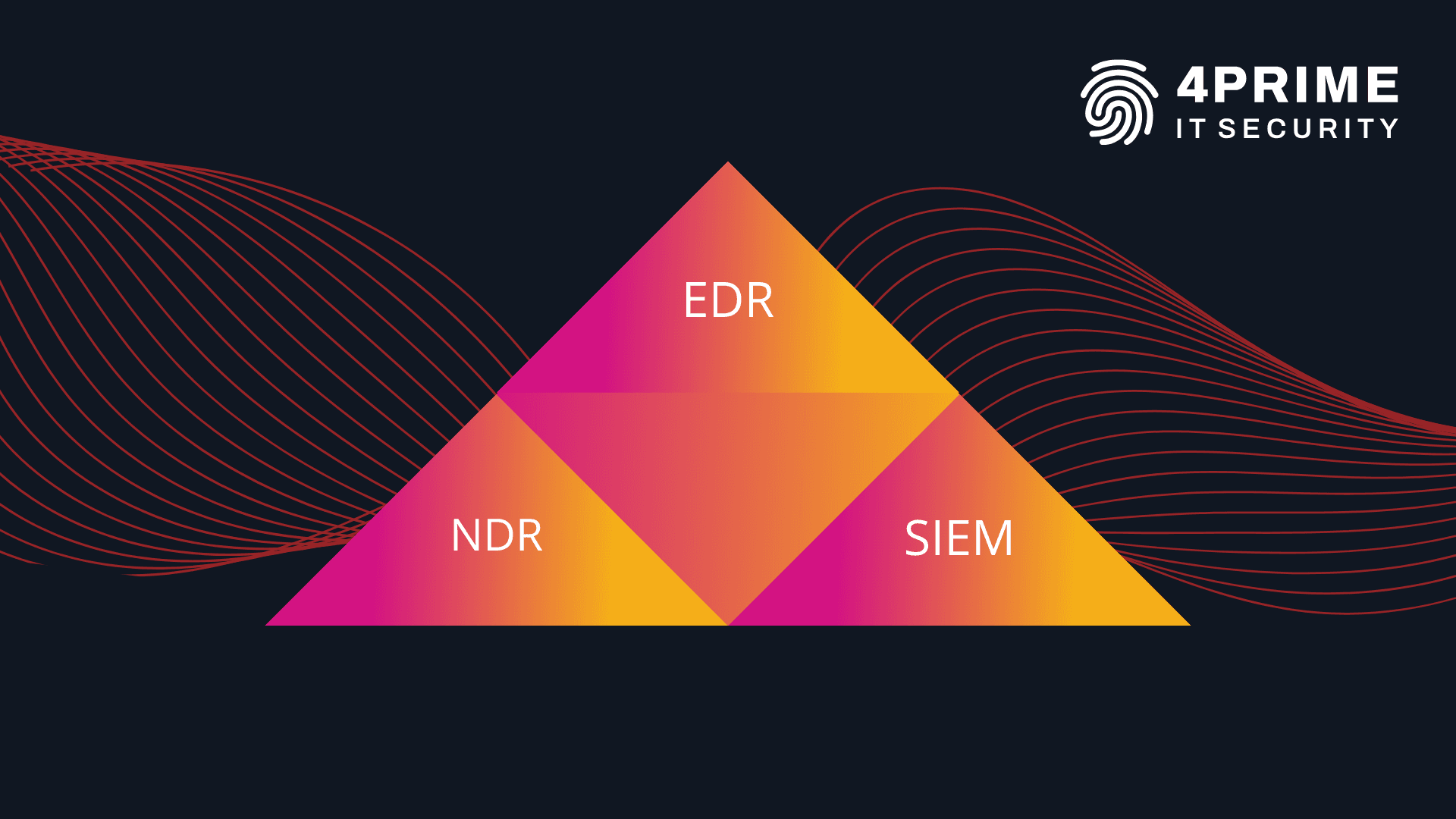
Our SOC360 team recommends the so-called SOC Visibility Triad, consisting of three integrated tools: EDR, NDR, and SIEM.
In this article, we explain why EDR and NDR should form the foundation of cybersecurity, and why SIEM—although a valuable complement to the architecture—does not fully meet the requirements of effective IT protection when used as a standalone tool.
EDR – Endpoint Detection and Response
If your organization has not yet implemented cybersecurity solutions or relies only on antivirus software and a firewall (NGFW), the first step should be the deployment of an EDR system. EDR focuses on monitoring and protecting network endpoints such as workstations, servers, and mobile devices.
Why is EDR the foundation of IT security? Because it addresses approximately 70% of attack techniques described in the MITRE ATT&CK matrix.
The core functions of EDR systems include:
a. Real-time threat detection – Thanks to built-in AI and Machine Learning (ML) mechanisms, EDR systems can quickly detect anomalies at the operating system level. These tools identify known threats, new attack techniques, and advanced methods of concealing malicious code, such as polymorphism or obfuscation.
b. Automated response and post-incident analysis – EDR systems automatically isolate infected devices, files, or processes immediately after detection. By collecting telemetry data, they help improve the protection of the IT infrastructure and support compliance with the NIS2 Directive, which requires incident reporting.
c. System rollback to a pre-attack state – This capability ensures business continuity, minimizes downtime, and reduces losses caused by security incidents.
NDR – Network Detection and Response
NDR is the core of network traffic protection. It combines advanced analytics with full visibility into an organization’s internal infrastructure. NDR effectively identifies issues related to misconfigurations, security policy violations, performance degradation, and new attack techniques.
The main functions of NDR systems include:
a. Storage of full network traffic telemetry – NDR systems significantly improve incident response effectiveness by creating threat detection models using AI and ML.
b. Network flow analysis – By working on a copy of network traffic, NDR systems collect hundreds of different metadata attributes from observed flows. They detect advanced threats originating both from internal and external networks.
c. Full visibility – NDR systems enable in-depth threat analysis through network environment visualization.
SIEM – Security Information and Event Management
SIEM serves as a central point for processing all IT security-related events within an organization. It operates by collecting, storing, and analyzing logs and data from various sources, such as network devices, servers, applications, and endpoints.
SIEM relies on predefined correlation rules and therefore struggles with modern, sophisticated attack techniques. In a world where most cybercriminals use custom-built, tailored, and obfuscated malware, SIEM alone is insufficient—we need advanced telemetry.
The core functions of SIEM systems include:
a. Log collection from multiple sources, such as firewalls, web application firewalls, domain controllers, applications, and other log-capable systems.
b. Correlation and event analysis – The system detects attack patterns and anomalies.
c. Alerting and reporting – SIEM sends automated notifications to security teams and provides post-incident analysis reports.
EDR vs. SIEM
Although SIEM can collect endpoint telemetry data, EDR clearly outperforms it in many areas:
- Cost and efficiency of telemetry data – Collecting large volumes of endpoint telemetry in SIEM generates high licensing costs. EDR solutions are more cost-effective and significantly optimize expenses.
- Self-protection and attack resilience (anti-tamper) – Log forwarding mechanisms to SIEM lack self-protection and can be easily disabled during an attack. EDR systems include advanced anti-tampering mechanisms.
- Active threat response – EDR actively isolates infected files, devices, or processes in real time, regardless of endpoint location. SIEM is passive—it analyzes data and generates alerts but does not provide immediate response.
- Direct endpoint detection and prevention – EDR operates directly on endpoints, enabling fast prevention, detection, and mitigation. SIEM may introduce delays, as detection occurs centrally.
- Intuitive data presentation – EDR presents data in a way tailored to endpoint telemetry. SIEM requires additional configuration to effectively visualize endpoint data.
NDR vs. SIEM
While SIEM analyzes logs from network devices, NDR provides more advanced capabilities for detecting and responding to threats in network traffic. Key advantages of NDR include:
- Richer network traffic data – NDR records far more detailed metadata for each connection (e.g., GCX systems collect over 90 metadata attributes per connection, while SIEM typically records only a few basic fields).
- Intuitive visualization and analysis – NDR offers fast filtering, searching, and drill-down capabilities, improving analyst efficiency during alert investigation and incident response.
- Advanced detection mechanisms – By analyzing richer datasets, NDR increases the likelihood of timely threat detection. SIEM detection is usually limited to basic correlation rules and reputation data.
- Scalability and real-time context – NDR monitors all network traffic in real time and identifies suspicious activity at application and protocol layers. SIEM, due to its reliance on logs, often provides only partial and delayed visibility.
SIEM as a Complement to a Cybersecurity Strategy
Despite the clear advantages of EDR and NDR, SIEM should not be excluded from an organization’s cybersecurity strategy.
Within the SOC Visibility Triad, SIEM acts as a log collector and supports analysts with contextual analysis for threat detection. By aggregating logs and events from devices, applications, and IT systems, SIEM provides a broad view of organizational activity.
It is also valuable in areas where EDR and NDR lack visibility, such as Active Directory environments.
By integrating SIEM with EDR and NDR, organizations achieve comprehensive visibility across all layers—from network traffic to endpoints—combined with in-depth threat analysis.
Comprehensive Cybersecurity Support for Your Organization
Selecting cybersecurity systems should be tailored to the specific nature of an organization’s operations. EDR is an excellent starting point, particularly for organizations with a large remote workforce. NDR, as a next step, is ideal for monitoring complex corporate networks, while SIEM ensures centralized management and correlation of security data in more mature IT environments.
If you are interested in implementing EDR, NDR, or SIEM solutions, or SOC as a Service—contact us.
This article was prepared by a 4Prime expert and subsequently edited with the support of artificial intelligence tools.
Text autor:
