NDR in practice – use cases and scenarios where EDR is no longer enough
TL;DR: NDR is a natural complement to EDR solutions, providing visibility where endpoint agents cannot be installed — such as OT systems, industrial devices, or legacy infrastructure. By analyzing network traffic, it helps detect threats such as lateral movement, ransomware attacks, phishing, and potential data exfiltration. NDR also analyzes internal network traffic, which helps identify anomalies and insider threats. The greatest value comes when NDR is combined with EDR and SIEM systems, enabling event correlation and faster incident response. At the same time, the effectiveness of NDR depends on proper deployment, tuning, and the expertise of the team analyzing the generated alerts.
Just a few years ago, discussions about IT security were largely focused on firewalls and antivirus solutions. Today, organizations are far more aware of both the scale of cyber threats and the capabilities offered by the market. It is now widely understood that effective protection cannot rely on a single tool — it requires a layered approach and full visibility into what is happening within the environment.
In practice, many organizations — including our clients — begin building their security posture by deploying EDR. This is a natural step, as most cyberattacks start at the endpoint level. However, EDR alone does not provide full visibility into the environment, and in many cases an agent cannot be installed on every device, which limits the scope of protection.
OT systems, industrial devices, and legacy infrastructure often prevent EDR deployment. The same applies to peripheral devices — even a seemingly harmless printer can become an attack vector. A modified component could analyze printed documents and send their contents to an external API. Without monitoring the network layer, such activity could remain completely unnoticed.
This is where NDR becomes essential — a solution that complements endpoint protection with network traffic analysis and enables the detection of threats in areas where agent-based approaches cannot be applied. In the following sections, we will present practical NDR use cases and scenarios where its deployment significantly improves an organization’s security posture.
When NDR Makes Sense and Where It Works Best
The key criterion is not the size of the organization or its architecture. NDR is most valuable in environments where organizations want deeper visibility into network traffic, enabling them to identify anomalies and detect threats beyond the capabilities of traditional endpoint tools.
However, it is important to remember that the effectiveness of any technology depends on how it is used. NDR delivers the best results when it is properly configured and aligned with the specific characteristics of the environment. Correct interpretation of data and continuous adjustment of system settings to evolving organizational needs are crucial.
For many companies, this means developing internal expertise or working with a partner who can help fully leverage the platform’s capabilities. When implemented correctly, NDR becomes a powerful tool for improving visibility and strengthening resilience against cyber threats.
That is why training and team preparation are key elements of every deployment. At 4Prime, we place strong emphasis on this aspect. We run dedicated two- to three-day training sessions tailored to the client’s environment and needs, covering both the platform’s architecture and practical console usage, including event analysis scenarios.
Not every organization will be an ideal candidate for traditional NDR deployment. Companies that rely heavily on SaaS models and move their infrastructure to the cloud — for example by using Microsoft 365 or SASE solutions such as Prisma Access — may encounter technical or operational challenges when implementing classic NDR. In such cases, an individual assessment is required to determine whether and how network traffic monitoring can be implemented in a cloud environment.
NDR Use Cases
1. Deep Network Traffic Analysis and Protocol Decoding
One of the key capabilities of the NDR solution from Fidelis Security is the ability to decode protocols and break down network traffic into its fundamental components. In practice, this provides significantly deeper visibility into communications compared to traditional tools such as firewalls, which can only analyze network traffic to a limited extent.
Fidelis goes even further by offering DLP capabilities that analyze the content of transmitted data and help detect sensitive information leaving the organization.
Such deep inspection generates large volumes of data, which makes proper system tuning a critical part of deployment. This involves designing alerting scenarios tailored to the client’s environment — for example detecting employees downloading unauthorized files from the internet, monitoring attempts to send national identification numbers outside the organization, or controlling the types of files sent via email.
2. Complementing EDR Protection
NDR often acts as a natural complement to EDR solutions. Although EDR systems can collect some network activity information, this data is typically supplementary and does not provide a full picture of communication flows.
NDR analyzes traffic directly at the network level, decoding protocols and revealing what actually happens in communication between systems.
This becomes particularly important during real attack scenarios. If an attacker gains access to a host, one of the first actions is often disabling or bypassing the EDR agent. In such cases, the organization loses visibility at the endpoint level.
However, NDR operates independently of the agent and continues to observe network traffic. This allows security teams to detect suspicious activity and respond to threats even after the EDR agent has been disabled.
3. Monitoring Email Communication and Protecting Against Phishing
Some NDR solutions also analyze the email communication path by integrating with email infrastructure and inspecting message content.
Through protocol decoding and data analysis, the system can detect sensitive information leaving the organization before the email even reaches its recipient.
In practice, many companies use this capability in a controlled model by enabling a quarantine mechanism. For example, if an accounting employee sends an email containing national ID numbers, the system may automatically quarantine the message, generate an alert, and forward it to an administrator for verification.
The administrator then decides whether to release or delete the message. This approach reduces the risk of data leaks without completely disrupting operational processes.
NDR also supports protection against phishing, malware, and ransomware. By analyzing network traffic and external communication, the system can detect connections to known phishing domains, suspicious behavior after clicking a malicious link, or attempts to communicate with command-and-control infrastructure.
4. Detecting Lateral Movement and Network Behavior Anomalies
One of the most important NDR capabilities is detecting lateral movement — a situation where an attacker, especially during ransomware campaigns, moves through the network after gaining initial access to one system.
NDR analyzes all internal traffic, including files transferred between hosts, which allows suspicious activity to be detected even during the early stages of an attack.
The system can identify unusual mass data transfers or communication attempts between network segments that have not previously interacted.
Solutions such as Fidelis and Greycortex also use built-in analytics and machine learning algorithms to build behavioral profiles of hosts and users based on historical network activity.
This allows the system to establish a baseline of normal activity — for example which systems a user typically accesses, during which hours they work, and which protocols they normally use.
If a deviation occurs — such as unusual network scanning, communication with previously unseen hosts, or a sudden increase in connections — the NDR system can generate an alert indicating a potential anomaly. Security teams or SOC analysts can then analyze the context and determine whether the activity represents a real security incident. This mechanism also helps detect insider threats.
However, behavioral analysis based on machine learning also introduces challenges. One of them is the number of false positives, especially during the early deployment phase or in dynamic environments. Proper implementation, tuning, and continuous adjustment to the organization’s environment are therefore critical.
Response Mechanisms in NDR
Response mechanisms in NDR can be implemented in different ways — for example through integration with firewalls or other security systems to automatically block communication with a compromised host.
In practice, however, many organizations approach full automation cautiously, fearing that incorrect automated decisions could disrupt business operations.
For this reason, a common operating model is for NDR to generate alerts and provide analytical context, while the final response decision is made by the SOC team or security administrators.
Integration with EDR
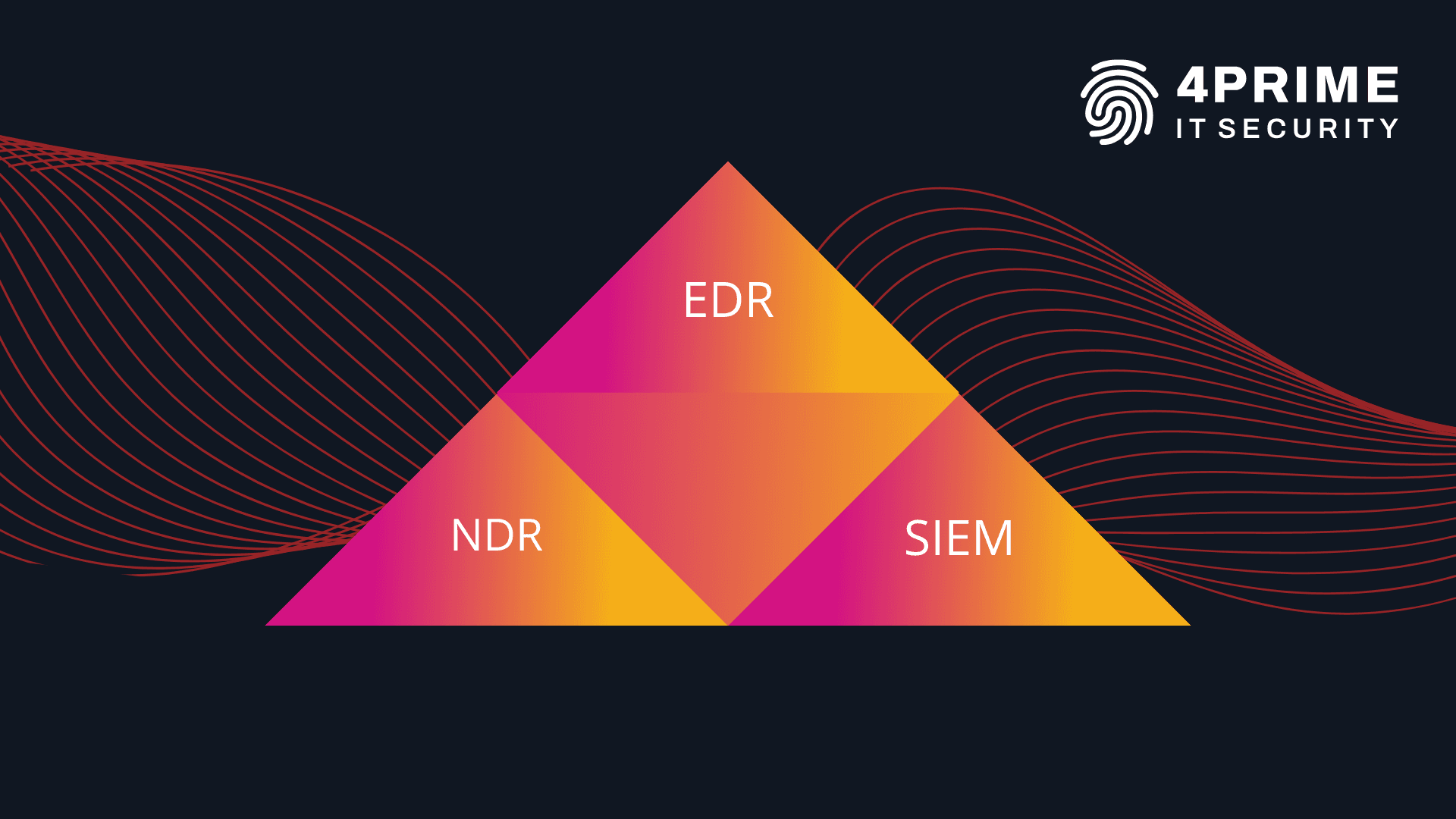
The full potential of NDR is revealed when it is combined with other security systems.
In practice, organizations often integrate EDR and NDR solutions to gain broader event context and visibility at both the endpoint and network levels.
For many of our clients, we integrate Fidelis NDR with SentinelOne or with Fidelis Endpoint, allowing events to be correlated and real threats to be identified faster.
Another approach is centralizing data within SIEM systems. As part of the SOC360 service, we integrate telemetry from EDR and NDR to create a unified view of incidents, automate analysis, and reduce response times. As a result, individual alerts are no longer isolated events but become part of a larger operational context, making it much easier to prioritize and respond effectively.
Popular NDR Solutions Used by Our Clients
Fidelis Security
Fidelis NDR provides advanced network visibility and deep communication analysis based not only on traditional DPI (Deep Packet Inspection) but also DSI (Deep Session Inspection).
This means the platform can reconstruct full communication sessions and analyze the context of entire interactions rather than just individual packets.
Organizations can therefore see exactly what happened during a session — which files were downloaded or uploaded (with the option to retrieve them), what data was transmitted, and how communication between systems occurred.
The platform also supports DLP functionality, allowing analysis of transmitted content and detection of attempts to exfiltrate sensitive data.
Fidelis also supports advanced threat detection through behavioral analysis and event correlation, helping identify lateral movement, data exfiltration attempts, and communication with command-and-control infrastructure.
An important extension of the platform is the Intercept module, which focuses on configuration hygiene, particularly within Active Directory environments. It helps detect weaknesses such as accounts with passwords that never expire — a common violation of organizational password policies.
Another noteworthy component is Fidelis Collector, which enables long-term storage and retrospective analysis of network traffic. Organizations can review historical data to determine whether a particular indicator of compromise (IOC) appeared in the environment earlier — even if it was not recognized as malicious at the time.
The solution allows the reconstruction of the entire attack chain: the source of the attack, communication methods, and how it spread through the network. Depending on configuration, data can be stored for up to a year, supporting advanced investigations and threat hunting activities.
Greycortex
Greycortex is an NDR solution focused on providing extensive network visibility and threat detection based on DPI (Deep Packet Inspection).
The platform performs detailed inspection of packets and network protocols, enabling the detection of suspicious behavior, communication anomalies, lateral movement attempts, and potential data exfiltration.
Greycortex incorporates advanced threat detection mechanisms using machine learning. By analyzing mirrored traffic from the core network, the Mendel platform provides an unprecedented level of visibility into monitored environments.
Mendel uses multiple advanced techniques including event correlation for predictive protection, flow analysis, and detailed packet inspection that allows threats such as malware and ransomware to be detected directly within network flows.
The platform is managed through an intuitive graphical interface that provides analytical and reporting modules for performance analysis and post-incident investigation during threat hunting processes.
Greycortex also offers strong scalability, making it suitable for a wide range of environments — from small businesses to complex enterprise infrastructures.
NDR Is a Process, Not a Product
NDR is a powerful tool that increases network visibility and enables detection of threats that remain outside the reach of traditional endpoint security solutions. However, technology alone does not guarantee security.
NDR generates large volumes of information, and its effectiveness depends on the expertise of the team responsible for interpreting alerts and adapting the system to the organization’s environment. This is where an experienced SOC team becomes essential.
The tuning process for NDR is continuous. The most intensive phase typically occurs at the beginning of deployment and can last up to a month, as it requires a deep understanding of the client’s environment, processes, and operational needs.
Later, ongoing maintenance and tuning become essential to ensure high-quality detections while minimizing false positives.
That is why at 4Prime IT Security we support clients not only during deployment but also through dedicated training, expert consulting, and our SOC services. Both 4Prime engineers and SOC360 analysts provide detection analysis services and help maintain the ongoing security of our clients.
Thanks to many years of experience in the cybersecurity industry, we act as a center of expertise, promoting and implementing best practices in threat detection across our clients’ environments.
If you want to learn how NDR can improve visibility and strengthen security in your organization, contact our expert who will help you select the right approach and solution for your environment.
Text autor: