Using the MITRE ATT&CK to build an effective cybersecurity strategy

Many organizations are still unfamiliar with MITRE ATT&CK, which means they do not understand the real techniques used in today’s cyberattacks. The scale of threats is growing exponentially, while at the same time companies often lack effective detection tools—or even awareness that they have already been compromised. MITRE ATT&CK is a practical map of adversary behavior and should be the foundation of any cybersecurity strategy. Understanding it enables a rational selection of technologies (EDR, NDR, SIEM), the construction of an effective SOC, and a shift from purely “after-the-fact” response (backups) toward real prevention and rapid incident response. Without this, cybersecurity remains superficial, and successful attacks will only continue to increase.
By mid-2024, CERT had received over 360,000 incident reports. This represents a significant increase considering that the total number of reports for all of 2023 was 80,000. Unfortunately, many companies—including our clients—still do not have adequate tools for threat detection, let alone mitigation. What’s more, a significant number of Polish organizations are not even aware that they are victims of cyberattacks.
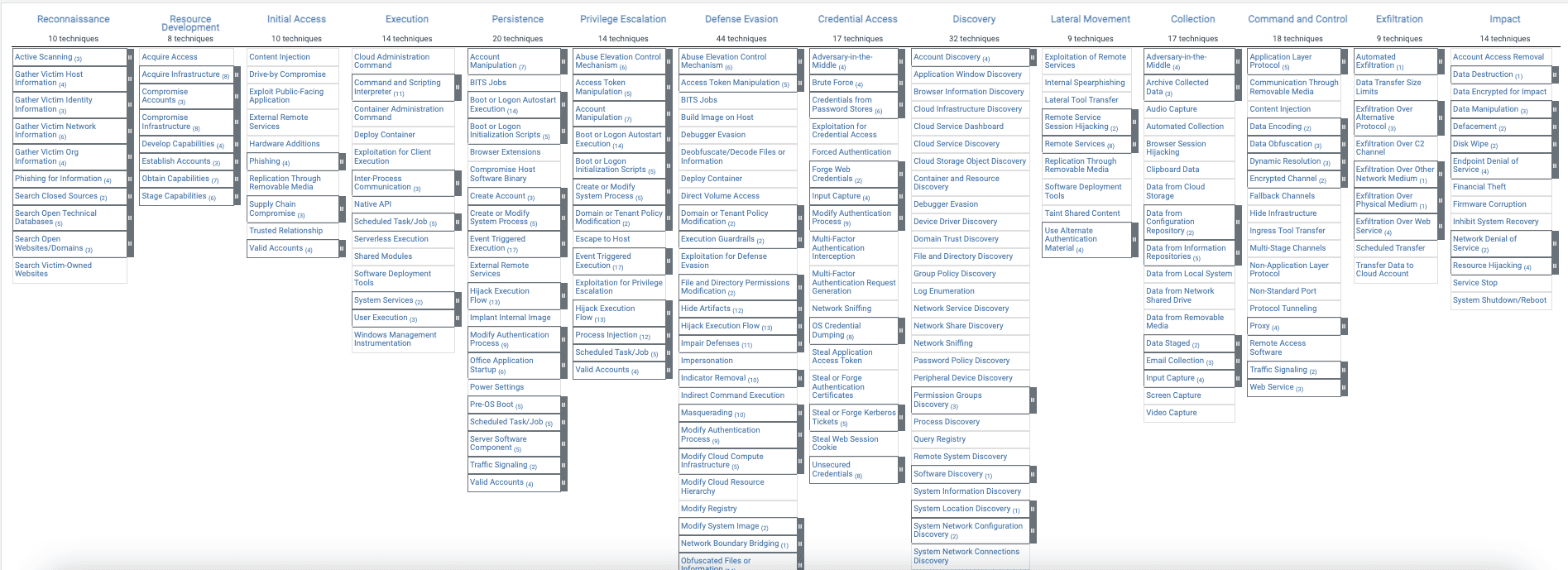
MITRE ATT&CK is a comprehensive repository of information on the techniques and tactics used by cybercriminals during attacks. The matrix provides insights that help organizations apply appropriate defensive strategies, minimizing the risk and impact of potential incidents. Understanding the MITRE ATT&CK matrix is crucial for building effective security systems in a conscious and structured way. It is therefore worth leveraging the potential of MITRE ATT&CK to develop an effective cybersecurity strategy.
What Is MITRE ATT&CK?
MITRE ATT&CK is a framework created by MITRE in 2013 to describe and categorize adversary behavior based on real-world observations. ATT&CK is a comprehensive repository of tactics, techniques, and procedures (TTPs) used by attackers, helping organizations better understand the threats they face. Thanks to this framework, security professionals can analyze incidents more effectively, plan defenses, and continuously improve security controls—ultimately increasing overall cyber resilience.
Using MITRE ATT&CK to Build a Cybersecurity Strategy
Analyzing and understanding the MITRE ATT&CK matrix supports multiple aspects of an organization’s cybersecurity strategy, including:
- Red Teaming: Simulating external attacks to identify weaknesses in systems and processes.
- Blue Teaming: Developing defensive strategies aligned with the tactics and techniques described in the matrix, improving incident response capabilities.
- Identifying critical points: Highlighting key areas that should be closely monitored.
- Selecting appropriate solutions that effectively detect and neutralize threats.
- Compliance management: Verifying whether selected technologies align with regulations and standards.
- Vulnerability discovery: Identifying weaknesses in infrastructure to enable remediation.
- Threat modeling: Anticipating potential attack scenarios.
- Identifying operational issues: Adjusting SOC processes and technologies to improve efficiency.
- Penetration testing planning: Defining areas that require in-depth security testing to continuously strengthen defenses.
Understanding MITRE ATT&CK and Selecting the Right Cybersecurity Tools
Given the growing number of cyber threats that can lead to serious incidents, understanding modern attack methods and deploying appropriate technologies is essential. This is driven not only by common sense but also by regulations such as the NIS2 Directive, which emphasizes the need for adequate technical measures aligned with current threats.
In the context of ransomware—currently among the most common attacks according to MITRE—organizations should seek solutions that effectively protect against data encryption. Yet we still encounter companies that rely solely on backups as their ransomware defense strategy. This means they are not attempting to prevent attacks but instead focus on restoring systems after an incident. This is surprising given that modern EDR systems are highly effective at detecting and stopping malicious encryption attempts. Such a cybersecurity strategy is a dead end.
Moreover, many organizations continue to use outdated antivirus solutions that have been ineffective since the widespread adoption of code obfuscation and polymorphic malware* (around 7–8 years ago), as well as SIEM systems that can detect only a handful of the hundreds of techniques listed in MITRE ATT&CK.
A lack of understanding of these nuances—and of the MITRE ATT&CK matrix itself—is one of the main reasons why effective cyberattacks continue to succeed and why we observe their rapid year-over-year growth.
So how can organizations protect themselves effectively?
* Polymorphism is a technique in which malware changes its underlying code to evade detection.
Solutions Addressing Attack Techniques Described in MITRE ATT&CK
EDR
Looking at the MITRE ATT&CK matrix, organizations may feel overwhelmed by the sheer number of documented attack techniques (201). The good news is that there is a single security solution that addresses approximately 70% of them: EDR (Endpoint Detection and Response), which protects endpoints and servers.
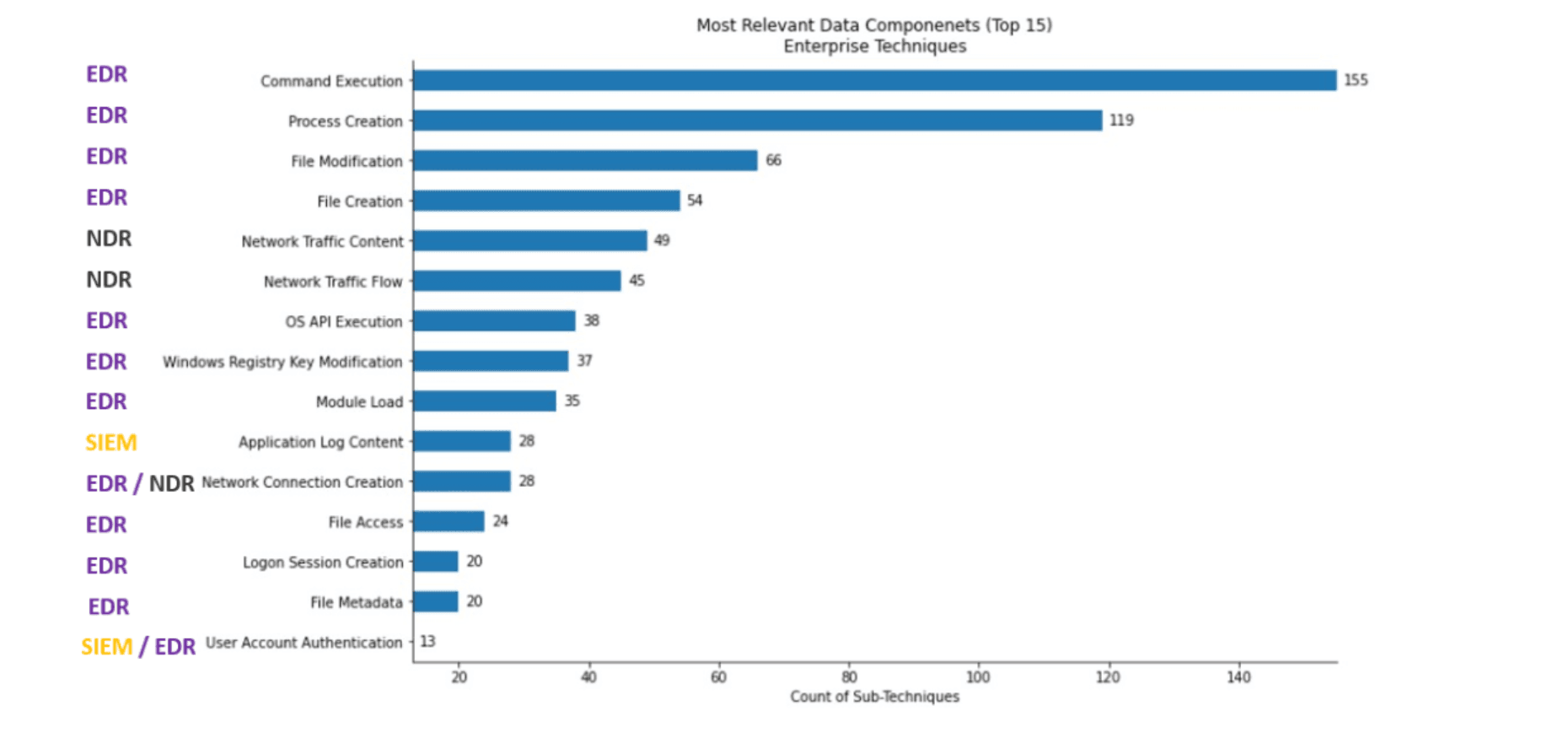
Our experience shows that while many endpoint security products market themselves as EDR, in reality a significant number lack key EDR capabilities—such as rollback functionality, which allows systems to be restored to a pre-attack state. When attacks modify system settings, memory, or the registry, organizations may be forced to manually repair or even reimage hundreds or thousands of machines.
Another critical factor when choosing an EDR solution is data presentation. An intuitive console with rich analytical tools and visualizations significantly improves analyst efficiency and response speed—both crucial during incidents. If a system generates thousands of alerts while providing only fragmented information, SOC analysts must seek confirmation from other tools, increasing response time and organizational risk. The choice of EDR therefore has a direct impact on overall security.
NDR
Based on the MITRE ATT&CK matrix, organizations should next consider implementing NDR (Network Detection and Response). NDR monitors all network traffic in real time, enabling detection of suspicious activity such as unusual connections or sudden large data transfers. By leveraging signatures and heuristics, NDR identifies attack techniques including lateral movement and data exfiltration. Behavioral profiling and rich network telemetry enable detection of unauthorized activity, while integration with EDR and SIEM provides full situational awareness.
However, having EDR, SIEM, and NDR is not enough—someone still needs to monitor them.
SOC
A Security Operations Center (SOC) plays a critical role in addressing the modern threats described in MITRE ATT&CK. SOC teams enable organizations to continuously monitor and analyze security incidents, as well as proactively detect and model threats based on adversary tactics and techniques.
By referencing the MITRE matrix, SOC teams can also identify infrastructure vulnerabilities, adjust detection and remediation mechanisms, detect misconfigurations, and better plan penetration tests. Leveraging MITRE ATT&CK makes SOC operations more effective in defending against complex cyber threats.
Learn how the SOC360 team operates.
An Effective Cybersecurity Strategy for Your Organization
As cyber threats continue to grow, understanding MITRE ATT&CK has become essential for organizations seeking effective protection. Deploying appropriate technologies such as EDR and NDR, combined with a well-functioning SOC, enables proactive detection and mitigation of attacks. Knowledge of attacker techniques allows organizations to build stronger defensive architectures—an absolute necessity in today’s rapidly evolving cybersecurity landscape.
Do you need SOC services, an EDR system, or NDR?
Contact us and we will help you implement an effective cybersecurity strategy for your organization.
This article was prepared by a 4Prime expert and subsequently edited with the support of artificial intelligence tools.
Text autor:
